Presentation
05 May 2018 / /
Using Teleport for Service Management
Teleport is an SSH system which we’ve fallen in love with. There are some great security features, of course:
- two factor authentication right out of the box
- acts as ssh certificate authority issuing short-lived credentials
- commercial options for role-based access control
But the features which we find most compelling are the ones you can’t get as easily with the likes of OpenSSH:
- session recording which can be used for audit or to refer back to from troubleshooting tickets
- session sharing so that our customers or junior staff can learn-by-doing, just like having dual controls on a car
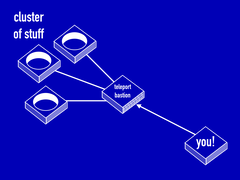
- NAT-piercing to help manage devices within customer networks that do not have direct Internet connectivity
We have been using Teleport on a number of projects and with several customers:
a remote probe deployment to debug a strange, intermittent connectivity problem (given as a talk at UKNOF 40 in conjunction with David Farrar of Exa Networks)
training sessions with customers’ technical staff to show them a slightly unusual systems administration request — and the resulting session recording is an excellent reference for next time their staff encounter a similar request for changes
paralleling pair programming we have been able to “observe” or “navigate” while junior staff “drive” the console to perform systems or network adminstration for the first time
I’ve evangelised Teleport because I feel its use fits with our philosophy of openness. Teleport could complement the knowledge sharing that goes on within network operations teams, and help senior staff work out the playbooks and improve operational procedures for their junior staff. At least one service provider was inspired by my longer Teleport presentation at NetMcr and set their junior staff the background task of moving all out-of-band access to their POP infrastructure to Teleport. I hope that their use of this tool empowers their junior engineers to take on more work, while satisfying any regulatory or audit requirements that security staff worry about.
As for the talk with David from Exa, my favourite moment was when he explained the root cause of the firewall issue. Watching from the side of the stage I could see the lightbulbs switching on in the audience’s heads as it clicked — spreading of clue, that’s what the conference is all about!
Read more about Teleport in my slides from the talk at UKNOF.